Dive into the world of IoT communication protocols where devices communicate seamlessly. From MQTT to CoAP, let’s explore how data travels in IoT systems.
Get ready to unravel the complexities and simplicities of IoT communication protocols that shape our connected world.
Internet of Things (IoT) Communication Protocols Overview
The concept of IoT communication protocols refers to the set of rules and standards that govern how devices communicate and exchange data in an Internet of Things (IoT) ecosystem. These protocols ensure seamless connectivity between various IoT devices, enabling them to transmit and receive information efficiently.
Importance of Communication Protocols in IoT Devices
Communication protocols play a crucial role in IoT devices by ensuring that different devices can understand each other’s data formats and transmit information accurately. Without standardized protocols, interoperability between devices would be challenging, leading to communication breakdowns and inefficiencies in IoT systems.
- Communication protocols establish a common language: By defining specific rules for data exchange, protocols enable devices from different manufacturers to communicate effectively.
- Enhanced security: Protocols include security measures to protect data transmitted between devices, safeguarding against potential cyber threats.
- Efficient data transmission: By streamlining the communication process, protocols help optimize data transfer, reducing delays and improving overall system performance.
- Scalability and flexibility: Standardized protocols support the scalability of IoT networks, allowing for the seamless integration of new devices and technologies.
Common IoT Communication Protocols

In the world of Internet of Things (IoT), communication protocols play a crucial role in ensuring devices can exchange data efficiently and securely. Let’s explore some of the popular IoT communication protocols and their features.
MQTT (Message Queuing Telemetry Transport)
MQTT is a lightweight messaging protocol designed for small sensors and mobile devices to communicate with IoT applications. It follows a publish/subscribe architecture, allowing devices to publish messages to a broker and subscribe to specific topics to receive relevant data. MQTT is known for its low bandwidth usage, making it ideal for IoT applications with limited resources.
CoAP (Constrained Application Protocol)
CoAP is a specialized web transfer protocol for IoT devices with limited processing capabilities and memory. It is designed to be simple and efficient, enabling devices to communicate over constrained networks such as UDP. CoAP supports request/response interactions between clients and servers, making it suitable for resource-constrained IoT devices.
HTTP (Hypertext Transfer Protocol)
HTTP is a well-known protocol used for communication between web servers and clients. While not specifically designed for IoT, HTTP is widely adopted and can be used in IoT applications that require interoperability with existing web services. However, HTTP may not be the most efficient choice for resource-constrained IoT devices due to its overhead.These IoT communication protocols vary in their features and functionalities, catering to different requirements of IoT applications.
MQTT is preferred for scenarios where low bandwidth usage is critical, CoAP is suitable for devices with limited resources, and HTTP can be used for interoperability with web services. Understanding the strengths and weaknesses of each protocol is essential in selecting the most suitable option for a specific IoT application.
Security Considerations in IoT Communication Protocols
IoT communication protocols play a crucial role in facilitating the exchange of data between connected devices. However, ensuring the security of these communication channels is paramount to protect sensitive information and prevent unauthorized access.
Importance of Security in IoT Communication Protocols
Security in IoT communication protocols is essential to safeguard the integrity, confidentiality, and availability of data transmitted between devices. Without adequate security measures, IoT networks are vulnerable to various cyber threats, including data breaches, malware attacks, and unauthorized access. By implementing robust security protocols, organizations can mitigate these risks and ensure the safe operation of their IoT systems.
Common Security Vulnerabilities in IoT Protocols
- Weak Authentication: Insecure authentication mechanisms can allow unauthorized users to gain access to IoT devices and networks.
- Insufficient Encryption: Lack of encryption can expose sensitive data to interception and tampering during transmission.
- Insecure APIs: Vulnerabilities in APIs used for communication between devices can be exploited to compromise the entire IoT network.
- Lack of Firmware Updates: Outdated firmware in IoT devices may contain known vulnerabilities that can be exploited by attackers.
Measures to Secure IoT Communication Channels and Data Transmission
- Implement Strong Authentication: Use secure authentication methods such as multi-factor authentication to verify the identity of users and devices.
- Encrypt Data: Utilize robust encryption algorithms to protect data in transit and at rest, ensuring confidentiality and integrity.
- Secure APIs: Implement proper access controls and authentication mechanisms to prevent unauthorized access to APIs.
- Regular Firmware Updates: Keep IoT device firmware up to date to patch known vulnerabilities and enhance security.
- Network Segmentation: Segment IoT devices into separate networks to limit the impact of a security breach and contain threats.
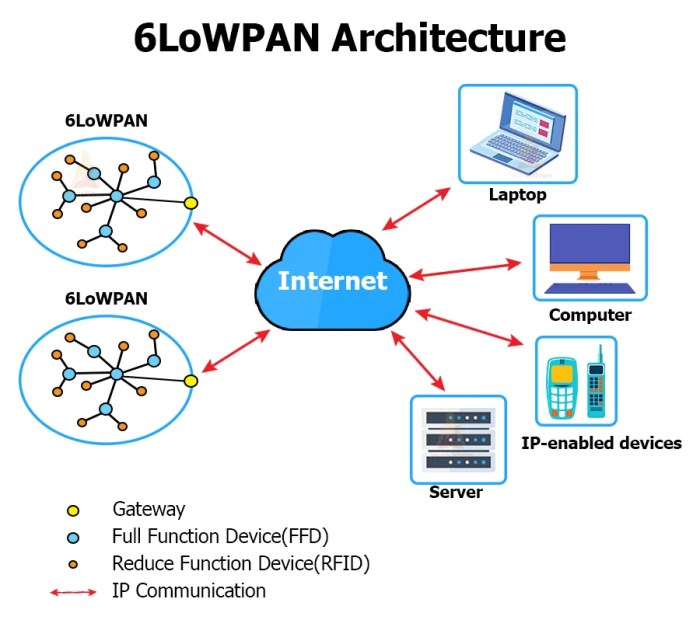
Interoperability Challenges in IoT Communication Protocols
Interoperability in IoT communication protocols refers to the ability of different devices and systems to communicate effectively with each other, regardless of the underlying protocols they use. This is a crucial aspect of IoT as it enables seamless integration and interaction between diverse devices in a network.Standardization efforts play a key role in addressing interoperability challenges in IoT. By establishing common protocols and communication standards, organizations aim to create a unified framework that allows devices from various manufacturers to communicate with each other without any compatibility issues.
Standardization Efforts for Interoperability
Standardization bodies such as the Institute of Electrical and Electronics Engineers (IEEE), International Organization for Standardization (ISO), and Internet Engineering Task Force (IETF) are actively working towards developing standardized protocols for IoT communication. These protocols define a set of rules and guidelines that ensure devices can exchange data and information seamlessly.
- One example of a standardized protocol is the Message Queuing Telemetry Transport (MQTT), which is designed for efficient communication between IoT devices. MQTT’s lightweight nature and publish-subscribe architecture make it ideal for IoT applications.
- Another widely used protocol is the Constrained Application Protocol (CoAP), which is specifically designed for resource-constrained IoT devices. CoAP enables these devices to communicate over the internet using a RESTful protocol.
- Standardization efforts also include the development of interoperability frameworks such as the Open Connectivity Foundation (OCF) and the Thread Group, which aim to define common standards for device discovery, security, and communication in IoT networks.
Impact of IoT Communication Protocols on Data Communication
IoT communication protocols play a crucial role in determining how data is transferred and exchanged among connected devices. These protocols not only facilitate communication but also impact the efficiency, speed, and security of data transmission in IoT networks.
Real-time Data Streaming and Analytics
- IoT communication protocols enable real-time data streaming, allowing devices to transmit and receive data instantaneously. This real-time capability is essential for applications that require immediate processing and decision-making.
- By utilizing protocols like MQTT or CoAP, IoT devices can continuously send data to centralized servers or cloud platforms for analysis. This enables real-time monitoring, predictive maintenance, and other data-driven insights.
- Efficient communication protocols ensure that data is transmitted without delays or bottlenecks, enabling seamless data streaming for analytics and visualization purposes.
Enhanced Scalability of IoT Networks
- IoT communication protocols play a key role in enhancing the scalability of IoT networks by optimizing data transfer and reducing network congestion.
- Protocols like HTTP, MQTT, or AMQP are designed to handle large volumes of data efficiently, allowing IoT networks to scale up without compromising performance.
- By implementing lightweight protocols and efficient data compression techniques, IoT devices can communicate effectively across large networks, supporting a growing number of connected devices and applications.
Computer Repair and Consulting
Computer repair and consulting firms offer a range of services to ensure that your computer systems are running smoothly and efficiently. They provide technical support, troubleshooting, maintenance, and consulting services to individuals and businesses.
Services Offered by Computer Repair and Consulting Firms
- Hardware diagnostics and repair
- Software installation and updates
- Virus and malware removal
- Data recovery and backup solutions
Importance of Regular Maintenance and Troubleshooting for Computers
Regular maintenance and troubleshooting are essential to keep your computer systems running smoothly and prevent potential issues. By performing routine maintenance tasks such as software updates, disk cleanup, and virus scans, you can ensure the optimal performance and longevity of your devices.
Role of Consulting Services in Optimizing Computer Performance
Consulting services play a crucial role in optimizing computer performance by providing expert advice and guidance on IT infrastructure, software solutions, and system integration. Consultants can help businesses identify and resolve technical issues, implement best practices, and streamline operations to enhance overall efficiency and productivity.
Data Communication
Data communication plays a crucial role in modern computing by enabling the exchange of information between devices or systems. It involves the transmission of data from one point to another, allowing for seamless connectivity and collaboration in today’s digital world.
Methods of Data Transmission
- Wired Communication: Involves physical connections such as cables or wires to transfer data between devices. Examples include Ethernet cables, USB cables, and fiber optics.
- Wireless Communication: Utilizes wireless signals to transmit data over the airwaves, eliminating the need for physical connections. Technologies like Wi-Fi, Bluetooth, and cellular networks fall under this category.
Impact of Data Communication Protocols
Data communication protocols are essential for ensuring efficient and reliable network operations. These protocols define the rules and conventions for data exchange, establishing a common language that devices must follow to communicate effectively. By adhering to these protocols, organizations can enhance network performance, minimize errors, and improve data security.
Computers E-Books
In today’s digital age, e-books have become increasingly popular, especially in the field of computer science and technology. These electronic versions of books offer numerous advantages for learning computer-related topics, making them a valuable resource for both beginners and experienced professionals alike.
Advantages of E-Books for Learning Computer-Related Topics
- Portability: E-books can be easily accessed on various devices such as laptops, tablets, and smartphones, allowing users to study anytime and anywhere.
- Searchability: E-books often come with search functionalities that enable users to quickly find specific information within the text, saving time and enhancing the learning process.
- Interactivity: Some e-books include multimedia elements, interactive quizzes, and links to external resources, providing a more engaging learning experience.
- Cost-Effectiveness: E-books are generally more affordable than printed books, making them a cost-effective option for students and professionals looking to expand their knowledge.
Popular E-Books Focusing on Computers and Technology
1. “Clean Code
A Handbook of Agile Software Craftsmanship” by Robert C. Martin – This e-book is a must-read for software developers looking to improve their coding practices and produce high-quality, maintainable code.
2. “The Phoenix Project
A Novel About IT, DevOps, and Helping Your Business Win” by Gene Kim, Kevin Behr, and George Spafford – This e-book offers insights into DevOps principles and practices through a fictional story, making it an engaging read for IT professionals.
3. “Python Crash Course
A Hands-On, Project-Based Introduction to Programming” by Eric Matthes – Ideal for beginners, this e-book provides a comprehensive introduction to Python programming through hands-on projects and exercises.
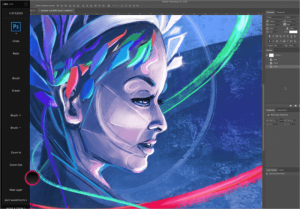
Graphics and Multimedia
Graphics and multimedia play a crucial role in enhancing user experience on computers by providing visually appealing and interactive content. They help in conveying information effectively and engaging users through a combination of images, videos, animations, and other visual elements.
Role of Graphics and Multimedia
Graphics and multimedia are essential components of modern computing systems, contributing to various aspects such as entertainment, education, communication, and design. They enable users to interact with the digital world in a more immersive and intuitive manner, making the overall computing experience more engaging and enjoyable.
- Graphics and multimedia enhance the visual representation of data, making it easier for users to interpret and analyze information.
- They enable the creation of interactive and dynamic content that captures users’ attention and encourages them to engage with the system.
- Graphics cards, displays, and multimedia software are essential for running multimedia applications such as video editing, gaming, graphic design, and 3D modeling.
Popular Multimedia Technologies
Multimedia technologies encompass a wide range of tools and formats that enable the creation, manipulation, and presentation of multimedia content. Some popular multimedia technologies used in computer systems include:
- Adobe Creative Suite: A collection of software applications for graphic design, video editing, and web development.
- Virtual Reality (VR) and Augmented Reality (AR) technologies: Immersive technologies that blend the physical and digital worlds to create interactive experiences.
- HTML5: A markup language used for creating multimedia-rich web content, including animations, audio, and video.
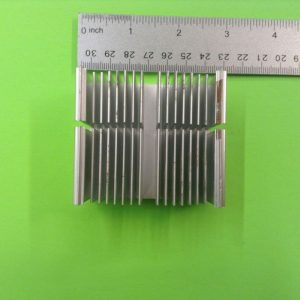
Computers Hardware
Computer hardware refers to the physical components of a computer system that allow it to function. These components include the CPU, GPU, RAM, and storage devices, among others. Each hardware component plays a crucial role in the overall performance of a computer.
Components of Computer Hardware
- The Central Processing Unit (CPU) is often considered the “brain” of the computer, responsible for executing instructions and performing calculations.
- The Graphics Processing Unit (GPU) is specialized in handling graphics-related tasks, such as rendering images and videos.
- Random Access Memory (RAM) serves as the computer’s short-term memory, storing data that is currently being used by the system or applications.
- Storage devices, like hard disk drives (HDDs) and solid-state drives (SSDs), store data for the long term, even when the computer is turned off.
Latest Trends in Computer Hardware Development
- Advancements in CPU technology, such as the development of multi-core processors, have significantly improved computing power and efficiency.
- GPU manufacturers are focusing on creating more powerful and energy-efficient graphics cards to cater to the growing demand for high-quality visuals in gaming and other applications.
- SSDs are becoming increasingly popular due to their faster read and write speeds compared to traditional HDDs, leading to overall performance improvements in computers.
Importance of Hardware Compatibility and Optimization
- Hardware compatibility ensures that all components of a computer work seamlessly together, preventing compatibility issues that could hinder performance.
- Optimizing hardware settings and configurations can enhance the overall efficiency of a computer system, maximizing its capabilities and improving user experience.
- Efficient hardware utilization is essential for tasks like gaming, video editing, and other resource-intensive activities, as it can directly impact performance and responsiveness.
Ultimate Conclusion
In conclusion, IoT communication protocols play a vital role in ensuring smooth data flow across devices, paving the way for a smarter and more interconnected future.
User Queries
Which IoT protocol is best for real-time data streaming?
MQTT is highly recommended for real-time data streaming due to its lightweight nature and efficient publish-subscribe model.
How can IoT communication protocols enhance network scalability?
By optimizing data transfer and ensuring efficient communication, IoT protocols contribute to the scalability of networks by handling increased data traffic effectively.
What are the common security vulnerabilities in IoT communication protocols?
Common vulnerabilities include insecure data transmission, lack of authentication, and susceptibility to DDoS attacks, emphasizing the need for robust security measures.